Mobile Threats Quick Response Codes Download Malicious Software
What are the Types of Malware?
While at that place are many dissimilar variations of malware, you are most likely to encounter the following malware types:
| | | |
|---|---|---|
| | | |
| | | |
| | | |
| | | |
| | | |
| | | |
| | | |
| | | |
| | | |
| | | |
Below, we describe how they piece of work and provide existent-world examples of each.
1. Ransomware
Ransomware is software that uses encryption to disable a target'south admission to its data until a bribe is paid. The victim organization is rendered partially or totally unable to operate until it pays, but in that location is no guarantee that payment will outcome in the necessary decryption key or that the decryption key provided will role properly.
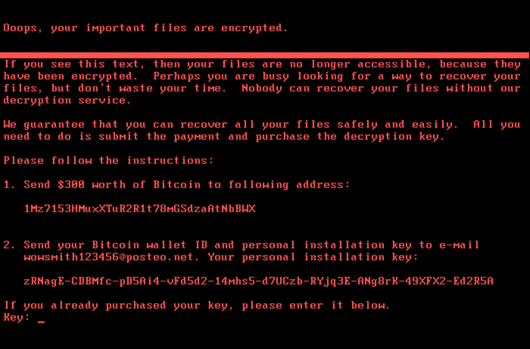
Example of a bribe letter
Ransomware Example:
This twelvemonth, the city of Baltimore was hit by a blazon of ransomware named RobbinHood, which halted all city activities, including tax collection, property transfers, and authorities email for weeks. This attack has cost the urban center more than $18 1000000 so far, and costs go along to accrue. The aforementioned blazon of malware was used against the urban center of Atlanta in 2018, resulting in costs of $17 one thousand thousand.
two. Fileless Malware
Fileless malware doesn't install anything initially, instead, it makes changes to files that are native to the operating system, such as PowerShell or WMI. Because the operating arrangement recognizes the edited files as legitimate, a fileless attack is non caught by antivirus software — and because these attacks are stealthy, they are upwardly to 10 times more than successful than traditional malware attacks.
Fileless Malware Instance:
Astaroth is a fileless malware campaign that spammed users with links to a .LNK shortcut file. When users downloaded the file, a WMIC tool was launched, along with a number of other legitimate Windows tools. These tools downloaded additional code that was executed simply in retention, leaving no testify that could be detected by vulnerability scanners. Then the attacker downloaded and ran a Trojan that stole credentials and uploaded them to a remote server.
Fileless Intrusions
Download our white paper to get a detailed anatomy of a fileless intrusion.
Download Now
3. Spyware
Spyware collects information nearly users' activities without their knowledge or consent. This tin include passwords, pins, payment information and unstructured messages.
The apply of spyware is not limited to the desktop browser: it tin can too operate in a critical app or on a mobile phone.
Even if the data stolen is non critical, the effects of spyware ofttimes ripple throughout the organization as functioning is degraded and productivity eroded.
Spyware Example:
DarkHotel, which targeted business concern and government leaders using hotel WIFI, used several types of malware in order to gain access to the systems belonging to specific powerful people. Once that access was gained, the attackers installed keyloggers to capture their targets passwords and other sensitive information.
iv. Adware
Adware tracks a user's surfing activity to determine which ads to serve them. Although adware is similar to spyware, it does non install whatsoever software on a user's reckoner, nor does information technology capture keystrokes.
The danger in adware is the erosion of a user's privacy — the information captured by adware is collated with information captured, overtly or covertly, about the user'due south activity elsewhere on the internet and used to create a profile of that person which includes who their friends are, what they've purchased, where they've traveled, and more than. That information tin be shared or sold to advertisers without the user's consent.
Adware Example:
Adware called Fireball infected 250 meg computers and devices in 2017, hijacking browsers to change default search engines and track web activity. Still, the malware had the potential to become more than a mere nuisance. Three-quarters of it was able to run code remotely and download malicious files.
Expert Tip
Download CrowdInspect: a free community tool for Microsoft Windows systems that is aimed to assist alert you to the presence of potential malware are on your computer that may be communicating over the network.Download CrowdInspect
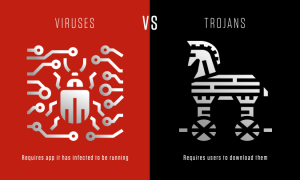
5. Trojan
A Trojan disguises itself as desirable code or software. Once downloaded by unsuspecting users, the Trojan tin can take control of victims' systems for malicious purposes. Trojans may hide in games, apps, or even software patches, or they may be embedded in attachments included in phishing emails.
Trojan Example:
Emotet is a sophisticated banking trojan that has been effectually since 2014. It is difficult to fight Emotet because it evades signature-based detection, is persistent, and includes spreader modules that aid it propagate. The trojan is so widespread that information technology is the subject of a United states Department of Homeland Security alarm, which notes that Emotet has price state, local, tribal and territorial governments upward to $i one thousand thousand per incident to remediate.
Learn More
TrickBot malware is a type of cyberbanking Trojan released in 2016 that has since evolved into a modular, multi-phase malware capable of a broad multifariousness of illicit operations. Learn more most what makes TrickBot highly concerning here.Read: What is TrickBot Malware
6. Worms
Worms target vulnerabilities in operating systems to install themselves into networks. They may proceeds admission in several means: through backdoors congenital into software, through unintentional software vulnerabilities, or through flash drives. Once in place, worms can be used past malicious actors to launch DDoS attacks, steal sensitive data, or bear ransomware attacks.
Worm Instance:
Stuxnet was probably developed past the US and Israeli intelligence forces with the intent of setting dorsum Iran's nuclear program. It was introduced into Iran'southward surround through a flash drive. Considering the environment was air-gapped, its creators never thought Stuxnet would escape its target's network — but it did. Once in the wild, Stuxnet spread aggressively but did footling damage, since its only function was to interfere with industrial controllers that managed the uranium enrichment process.
Acquire More than
Want to stay upwards to appointment on recent adversary activities? Stop by the Research and Threat Intel Weblog for the latest inquiry, trends, and insights on emerging cyber threats.Research and Threat Intel Weblog
7. Virus
A virus is a slice of lawmaking that inserts itself into an awarding and executes when the app is run. In one case within a network, a virus may be used to steal sensitive data, launch DDoS attacks or conduct ransomware attacks.
Viruses vs. Trojans
A virus cannot execute or reproduce unless the app it has infected is running. This dependence on a host application makes viruses different from trojans, which require users to download them, and worms, which do non utilise applications to execute. Many instances of malware fit into multiple categories: for instance, Stuxnet is a worm, a virus and a rootkit.
8. Rootkits
A rootkit is software that gives malicious actors remote control of a victim'due south estimator with total administrative privileges. Rootkits can exist injected into applications, kernels, hypervisors, or firmware. They spread through phishing, malicious attachments, malicious downloads, and compromised shared drives. Rootkits can also be used to conceal other malware, such as keyloggers.
Rootkit Case:
Zacinlo infects systems when users download a faux VPN app. Once installed, Zacinlo conducts a security sweep for competing malware and tries to remove information technology. So it opens invisible browsers and interacts with content like a human would — by scrolling, highlighting and clicking. This activity is meant to fool behavioral assay software. Zacinlo's payload occurs when the malware clicks on ads in the invisible browsers. This ad click fraud provides malicious actors with a cut of the commission.
Larn More
Blog Post on Machine Learning & Malware Defense: Learn where motorcar learning can exist nearly valuable and serve as an effective tool against both known and unknown malware. Read Blog
ix. Keyloggers
A keylogger is a type of spyware that monitors user activeness. Keyloggers accept legitimate uses; businesses tin employ them to monitor employee action and families may apply them to proceed runway of children's online behaviors.
However, when installed for malicious purposes, keyloggers can be used to steal password data, banking information and other sensitive data. Keyloggers tin be inserted into a system through phishing, social engineering or malicious downloads.
Keylogger Example:
A keylogger called Olympic Vision has been used to target Usa, Centre Eastern and Asian businessmen for business electronic mail compromise (BEC) attacks. Olympic Vision uses spear-phishing and social engineering techniques to infect its targets' systems in society to steal sensitive data and spy on business transactions. The keylogger is non sophisticated, simply it'south available on the black marketplace for $25 so it'southward highly attainable to malicious actors.
2022 CrowdStrike Global Threat Report
Download the 2022 Global Threat Report to detect out how security teams tin can better protect the people, processes, and technologies of a modern enterprise in an increasingly ominous threat landscape.
Download At present
10. Bots/Botnets
A bot is a software application that performs automated tasks on command. They're used for legitimate purposes, such equally indexing search engines, only when used for malicious purposes, they take the form of self-propagating malware that can connect back to a central server.
Ordinarily, bots are used in large numbers to create a botnet, which is a network of bots used to launch wide remotely-controlled floods of attacks, such as DDoS attacks. Botnets can become quite expansive. For example, the Mirai IoT botnet ranged from 800,000 to 2.5M computers.
Botnet Example:
Echobot is a variant of the well-known Mirai. Echobot attacks a wide range of IoT devices, exploiting over 50 dissimilar vulnerabilities, but information technology also includes exploits for Oracle WebLogic Server and VMWare'due south SD-Wan networking software. In improver, the malware looks for unpatched legacy systems. Echobot could be used by malicious actors to launch DDoS attacks, interrupt supply chains, steal sensitive supply chain information and carry corporate sabotage.
11. Mobile Malware
Attacks targeting mobile devices have risen l percent since last year. Mobile malware threats are as various equally those targeting desktops and include Trojans, ransomware, advertising click fraud and more. They are distributed through phishing and malicious downloads and are a item problem for jailbroken phones, which tend to lack the default protections that were part of those devices' original operating systems.
Mobile Malware Case:
Triada is a rooting Trojan that was injected into the supply chain when millions of Android devices shipped with the malware pre-installed. Triada gains access to sensitive areas in the operating system and installs spam apps. The spam apps display ads, sometimes replacing legitimate ads. When a user clicks on one of the unauthorized ads, the acquirement from that click goes to Triada'south developers.

Mobile Threat Report
Download the latest mobile threat written report to explore why the targeting of mobile platforms is beingness increasingly adopted
Download Written report
Malware Detection and Removal with CrowdStrike
The best arroyo to protect against malware is to employ a unified array of methods. Machine learning, exploit blocking, whitelisting and blacklisting, and indicators of attack (IOCs) should all be part of every organization'southward anti-malware strategy.
CrowdStrike Falcon combines these methods with innovative technologies that run in the cloud for faster, more up-to-the-minute defenses.
The CrowdStrike Falcon platform gives analysts and threat researchers rapid and comprehensive malware search capabilities through access to the largest and nigh agile repository of threat events and artifacts in the industry. The repository contains a 300TB collection with over 400 1000000 files and indexes over ii trillion events each week.
All of this data is available for real-time search — both metadata and binary content — made possible within seconds past patent-pending indexing technology.
Deep analysis of evasive and unknown threats is a reality with Falcon Sandbox. Falcon Sandbox enriches malware search results with threat intelligence and delivers actionable IOCs, so security teams can better empathise sophisticated malware attacks and strengthen their defenses.
To battle the growing threat of mobile malware, organizations need visibility into which devices are accessing their networks and how they're doing information technology. CrowdStrike's Falcon for Mobile delivers mobile endpoint detection and response with existent-time visibility into IP addresses, device settings, WIFI and Bluetooth connections, and operating system data.
Want to see how the CrowdStrike Falcon Platform blocks malware? Start a free trial and see how it performs against alive malware samples.
Kickoff Free Trial
DOWNLOAD HERE
Posted by: adriennepubleausing.blogspot.com
Post a Comment